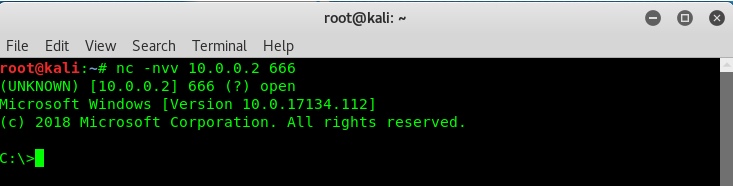
Do They Really Catch? | DNS Tunneling Vendor Test Series - Palo Alto NGFW | Ultra-slow & Heuristic - YouTube

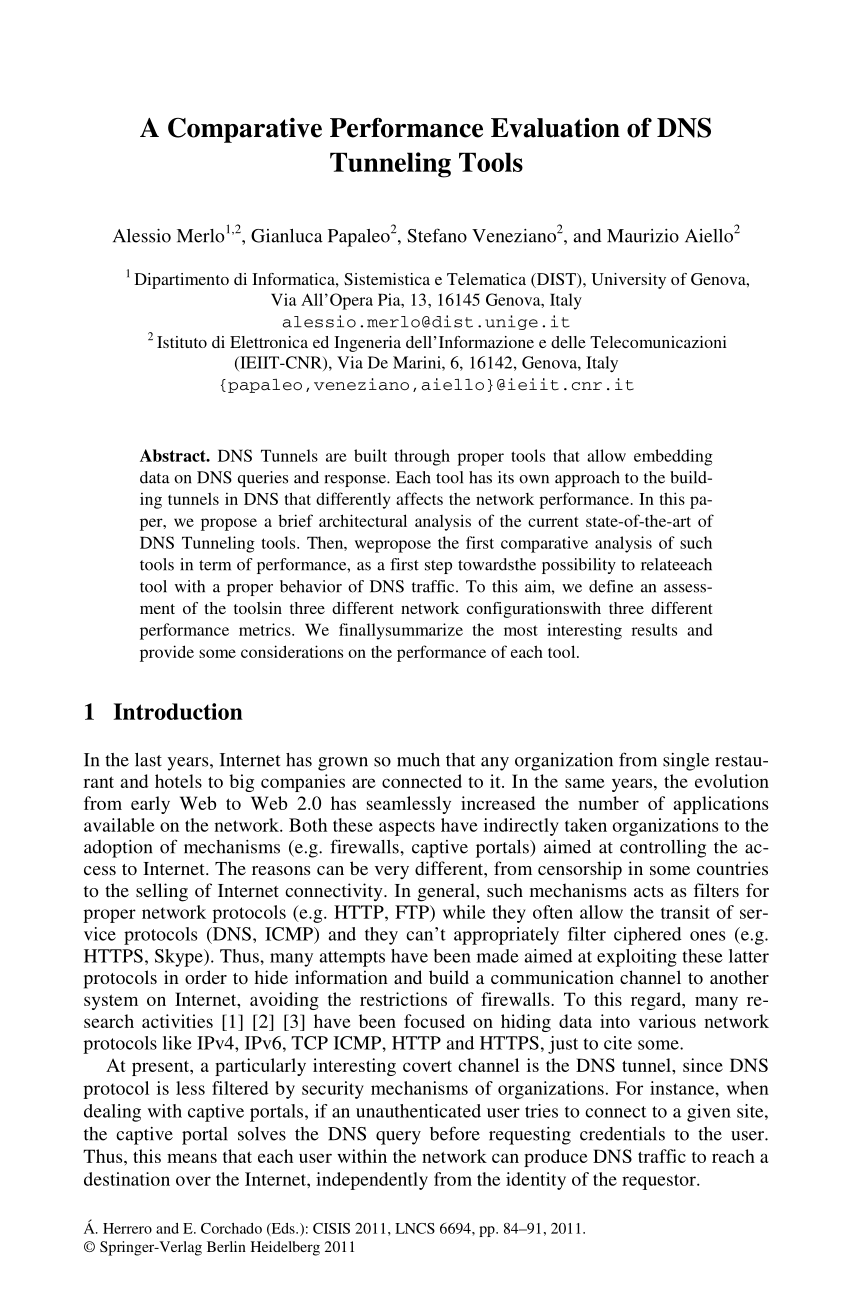
Identifying Malicious DNS Tunnel Tools from DoH Traffic Using Hierarchical Machine Learning Classification | SpringerLink
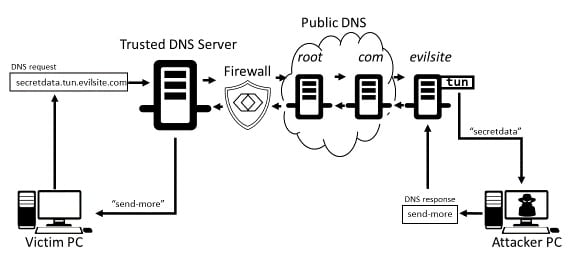
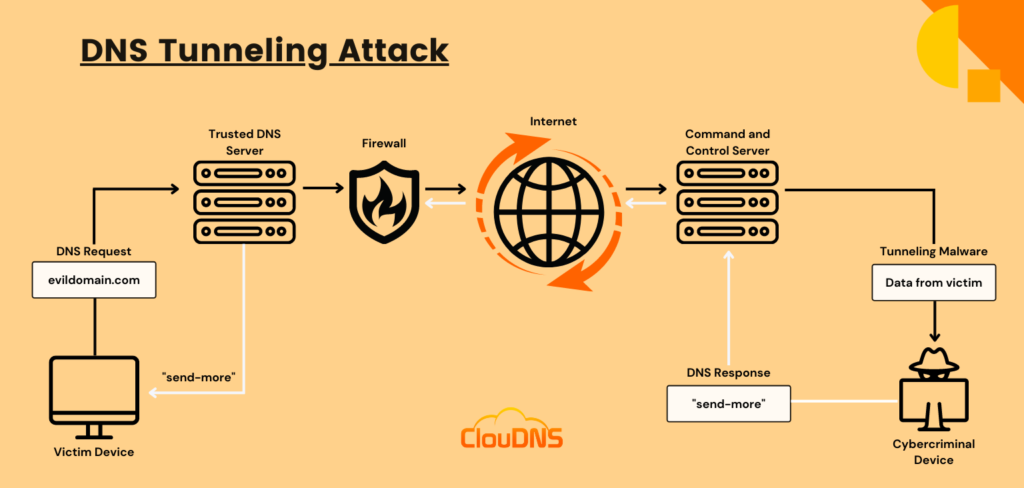
Electronics | Free Full-Text | Real-Time Detection System for Data Exfiltration over DNS Tunneling Using Machine Learning
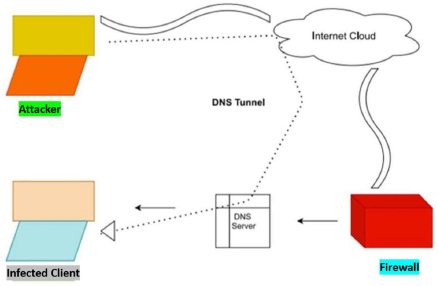
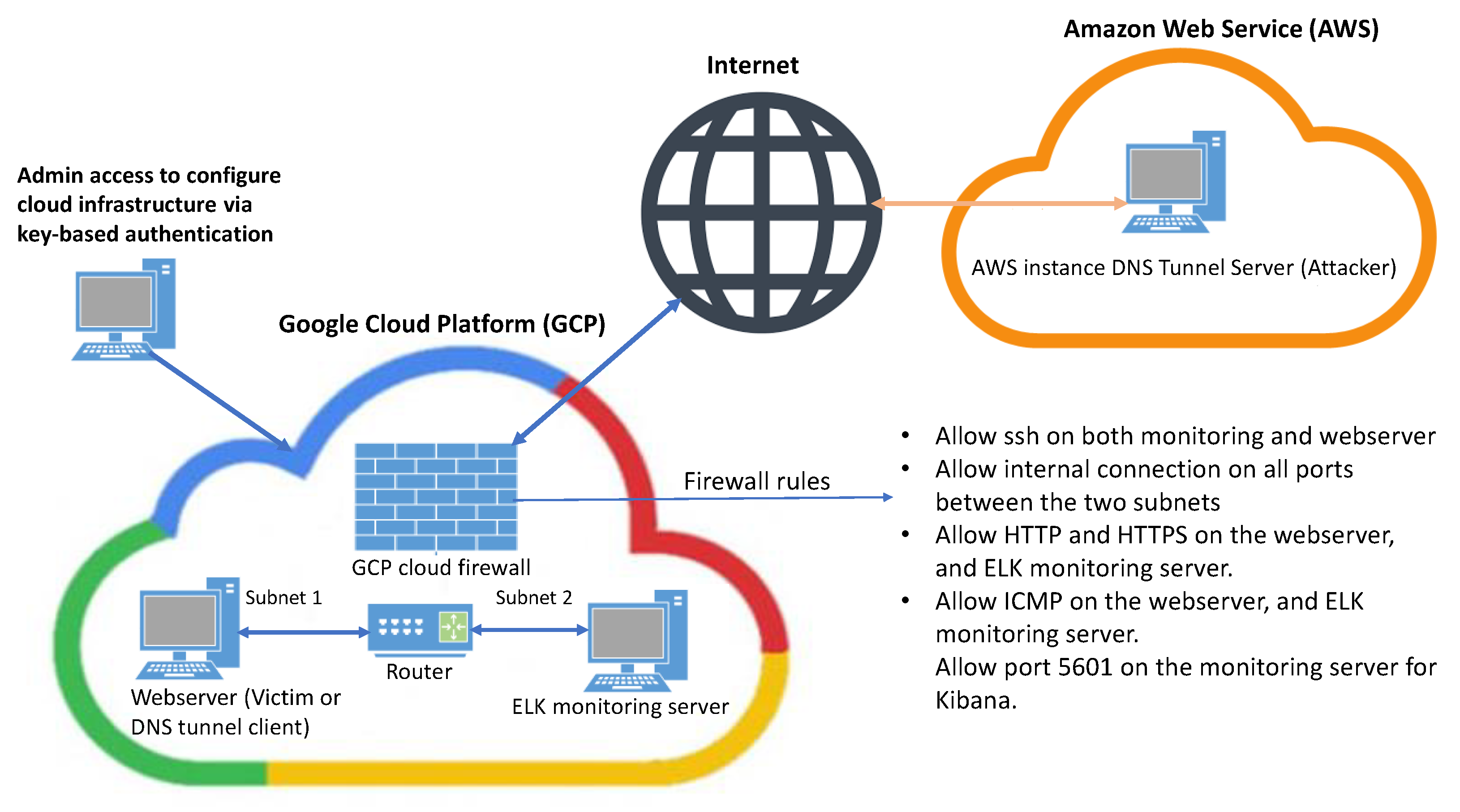
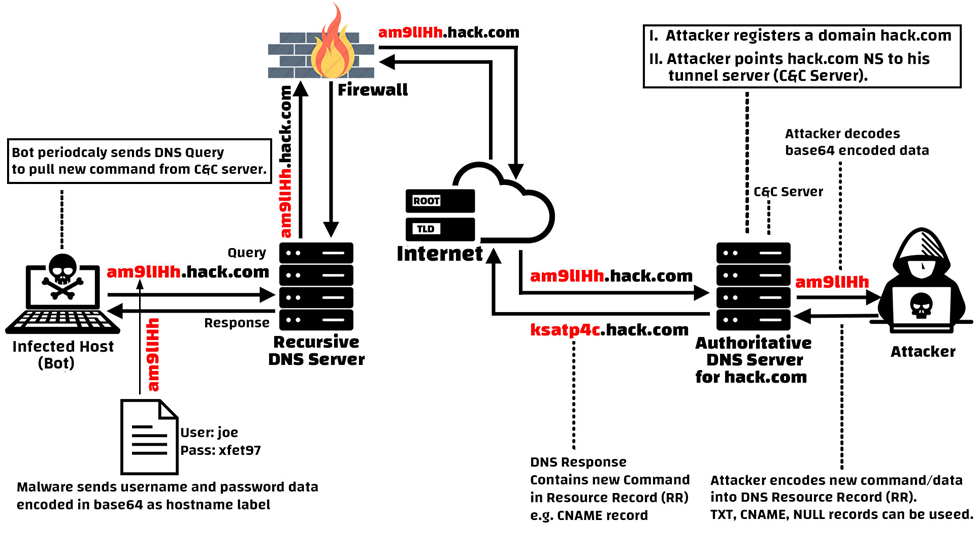
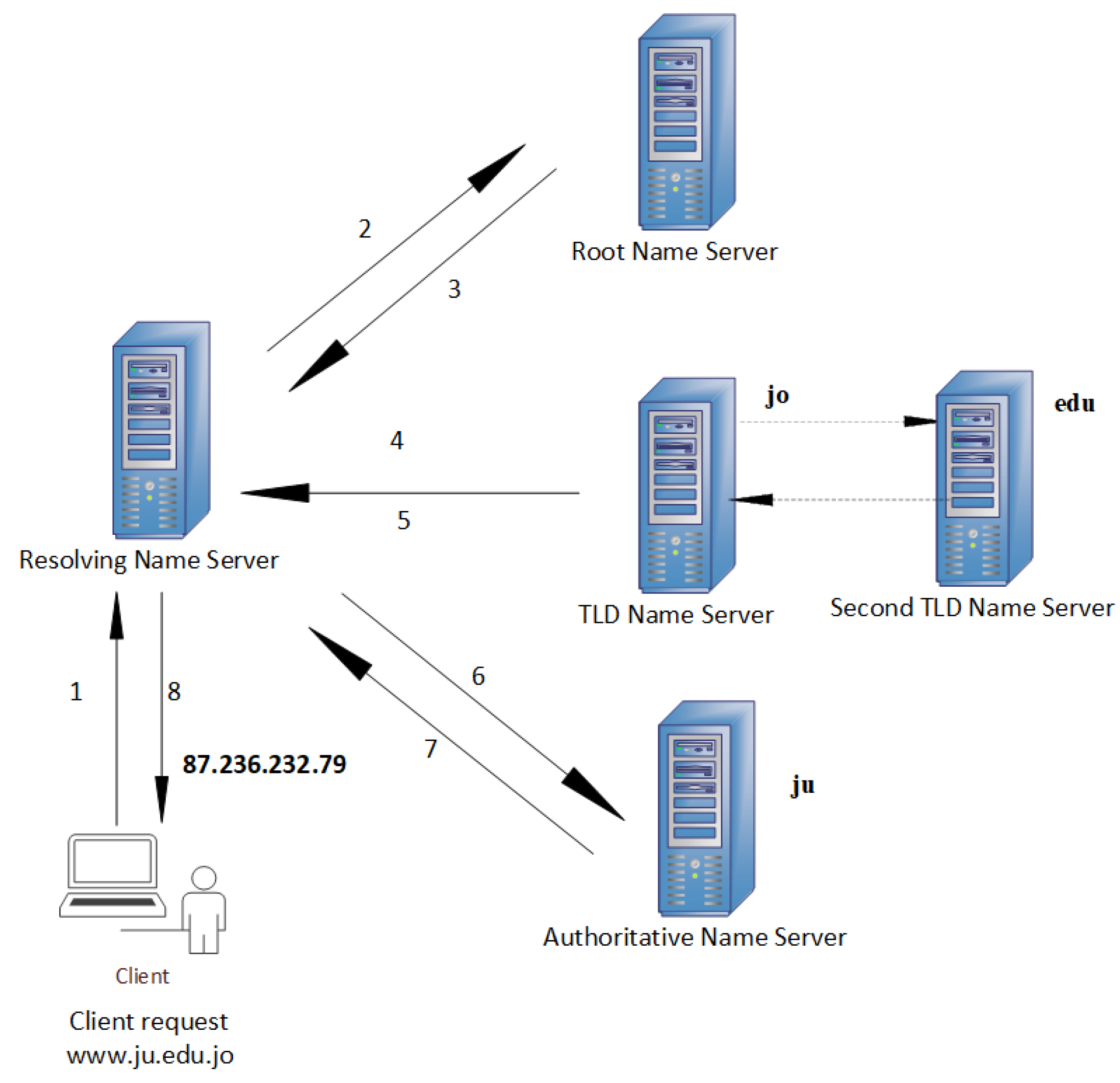
DNS Tunneling Simulation Topology 3.1. Log aggregation and simulation.... | Download Scientific Diagram